It is time to take off the kid gloves: do not download codecs!
It is time to take off the kid gloves: do not download codecs!The malware writers are having a grand old time introducing one rogue-infesting software after another, all because people fall into their trap -- they *must* watch that video and download the codec, Presto! The result is pop-ups, browser hijacks, and more.
Just take a peek over at the recent postings of the latest rogues over at Security Cadets. Yesterday, jahewi posted about the latest, a "remake" of VirusBurst/VirusBurster as "Virusbursters". The colder October weather has not resulted in a slow-down of variants either. S!Ri, the developer of the SmitfraudFix tool commonly used to remove the rogues has updated his software at least 14 times during October.
Unfortunately, the problem is not limited to codecs. The curious cannot resist and click on the link in an email, they open the e-card. Never mind that they don't know the sender of the e-mail or e-card. Curiosity gets the better of them -- and makes a mess of their computer. As Microsoft MVP Janie Whitty, known as CalamityJane, points out at BroadbandReports:
"Security Forums have been deluged with daily cries of help from victims of the "Smitfraud" desktop hijackers that are using fake codec to infect their prey.Although instructions are available in "Removing Fake Security Programs Like VirusBurst, WinMedia & other Codecs" for obtaining relief from these infections, there may be other lingering problems that need addressing. It would certainly be much easier to avoid the infection in the first place.
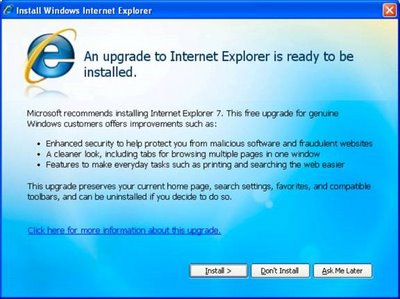
Watch out for the Zlob Trojan that poses as a codec needed to view a video, then installs a fake virus and urges its victims to download a rogue anti-spyware program to remove it. It has been confirmed that this malware also takes advantage of unpatched systems using exploits on web pages. Visit Microsoft Update to ensure that you have ALL of the critical Windows security updates!
»update.microsoft.com/microsoftupdate/
Other victims have been infected by a fake e-card greeting, or even a spoofed e-mail that claims to be Windows Update (Microsoft never sends updates via e-mail). Still more unassuming victims received an e-mail asking them to open a link to see the message (these can be fake e-mails, intended only to infect), or even a link from your 'buddy' in instant messages - but don't trust it if you aren't expecting it. Even your buddy could be infected without his/her knowledge and the virus on their computer is sending you the link with one purpose, and one purpose only - to infect you!"
Once again, the warning, as so aptly stated by Janie:
"If you receive a link for a video that says you need a certain codec in order to view it, be careful! Today, it could be a fake codec that is actually a Trojan just waiting to infect your system."